By way of disclosure, I am something of a Civil Liberties fanatic, and am firmly convinced that Obama did the wrong thing on retroactive immunity and am angry about that. Also, I haven't trusted George W. Bush since the first 10 secs I saw him speaking. He reminded me of the arrogant lying bullies who used to break my bones when I was a youngster. He set off all my alarms just by the way he talked and moved.Obama was something like my 4th choice in the primaries, ahead of Clinton.
So, I'm not an apologist for any of the current crop of politicians, and not at all well disposed towards anything that looks to weaken the rule of law, the Constitution or our civil liberties. All that being said, the brouhaha over FISA and the accusations of cowardice, lack of principles and political opportunism has started sounding a whole lot more like heat than the light of reason. A recent claim claim by Lawrence Lessig, a Civil Libertarian with a background in law made me stop and think.
[Obama's] vote for the FISA compromise is thus not a vote for immunity. It is a vote that reflects the judgment that securing the amendments to FISA was more important than denying immunity to telcos. Whether you agree with that judgment or not, we should at least recognize (hysteria notwithstanding) what kind of judgment it was. The amendments to FISA were good. Getting a regime that requires the executive to obey the law is important.
People on the left, people like Glenn Greenwald, Jonathan Turley, Russ Feingold and Chris Dodd keep painting the recent FISA as a false compromise, a capitulation to Bush, and a blot on the fourth amendment. So why do Lessig and former Constitutional Law lecturer Obama say that it is important? Who is right?
Well either you can pick your authority figure and believe them—you pays your money and you takes your chances—or roll up your sleeves, wade into the bill and make your own decision. I never was the "argument from authority" type. So why should I pick one camp or the other?
I've been working on this posting for more than a week, and I think I have a handle on a line of reasoning that shows that the FISA amendment makes sense and may very well be a "Good Thing™". I don't find the argument compelling, but I think that it really deserves to be fully explicated, discussed and weighed, and as of yet, I think that I can respect and understand anyone who feels either that it outweighs the argument that FISA as a whole or as amended is so damaging to civil liberties and the rule of law that it outweighs the benefit or the other way around. I would really like to hear people who are passionate on both sides after they understand this reasoning.
Assumptions
There are a number of assumptions regarding the level of protection that should be afforded communications depending upon the people and jurisdictions involved. In terms of the three major combinations, the following breakdown seems to by the default assumption:
- Spying on foreign/foreign communications is OK.
- Intercepting US/US communications requires a warrant or constitutional equivalent.
- Intercepting US/foreign communications is the purview of the FISA court and law
- The location where the spying is done is not as important as who is communicating.
In the next couple of subsections, I will lay out each of these, at least briefly.
1. Spying is OK
Some would argue that "spying is important" or even "spying is necessary". For the purposes of this analysis, all we need to assume is that it is legitimate for the foreign intelligence services to spy on foreigners when that is in keeping with their mission, our relationship to the foreign nations involved, so long as they do so in accordance with their regulations and charter. Such spying is conducted beyond the jurisdiction of the United States and beyond the guarantees of our constitution. Thus "foreign/foreign" communication, by which I mean communications between two people, neither of whom is a "US person", should not be controlled by US warrants or restricted by Constitutional rights. International laws may apply.
It is certainly possible to disbelieve in spying, but we have done foreign spying for a very long time and the foreign intelligence services have always been unencumbered by the US courts and Constitution, so long as they were operating outside the US and the subjects were foreigners.
2. US/US requires a warrant
On the other hand, spying on Americans in America requires a court order. In essence, whenever the US Constitution is the ruling law, Warrants are required, otherwise it is "unreasonable search and seizure". The simplest version of this is communications between two US citizens, in the US, but resident aliens in the US are by precedent also protected by the Constitution. The term "US persons" is used in many laws as a shorthand for US citizens, US resident aliens and US corporations, since corporations are generally treated as "persons" in US law at present. For the purposes of FISA, "US person" is defined as follows:
“United States person” means a citizen of the United States, an alien lawfully admitted for permanent residence (as defined in section 1101 (a)(20) of title 8), an unincorporated association a substantial number of members of which are citizens of the United States or aliens lawfully admitted for permanent residence, or a corporation which is incorporated in the United States, but does not include a corporation or an association which is a foreign power, as defined in subsection (a)(1), (2), or (3) of this section.
The requirement for warrants is a fundamental right in America, and the Constitution specifically limits the power of the government within its jurisdiction. There are certain questions about where the Constitution holds sway, but it at the very least applies within the sovereign jurisdiction of the United States and in all dealings between the US government and US citizens regardless of location.
3. FISA controls US/foreign surveillance
One may think, either as a civil libertarian or as a proponent of a strong federal executive that FISA in principle is bad law, but since 1978 in order to balance the government's legitimate foreign intelligence interests with the need for judicial oversight, FISA has been the law. It's basic charter is to control spying that occurs between US persons and foreign powers or agents. The simple Wikipedia summary of FISA is pretty much in keeping with my understanding and reads as follows:
The act was created to provide Judicial and congressional oversight of the government's covert surveillance activities of foreign entities and individuals in the United States, while maintaining the secrecy needed to protect national security. It allowed warrantless surveillance within the United States for up to one year unless the "surveillance will acquire the contents of any communication to which a United States person is a party". If a United States person is involved, judicial authorization was required within 72 hours after surveillance begins.
In short, if no US person is involved, even if the surveillance occurs within the US, assumption #1 applies, if a foreign agent power and US person are both involved, a FISA order is required. If no foreign agents or powers are involved, assumption #2 rules. FISA arose because the line between all-foreign and all-US can be blurry. FISA adds assumption #3 as the middle ground.
4. Location is now unimportant
When the mindset behind FISA was formed, location was pretty much static. If you were spying on two foreigners who were outside the US, you pretty much could be assumed to be outside the US. If you were listening to the conversation between two Americans who were inside the US, then you were probably there, too.
Today, this is less true. Main communications lines are often centered in the US and communications between foreign locations can often be picked up in the US. Similarly, Internal US communications may very well travel outside the US
en route. It is generally assumed that this shouldn't change the situation
vis a vis rights and Constitutional protections. The US government shouldn't be able to spy on Americans who are in America just because the act of spying occurs outside the US. Likewise, if traffic between known terrorists in Pakistan and agents in Spain happens to flow through the United States, the CIA should be as free to spy on it would have been if the bits/electrons had never crossed over our borders.
This is at the heart of the "FISA must be modernized to keep up with technology" argument that you often hear. And generally, I think that it is correct. The rights and protections should be determined primarily by who the actors are and who the subjects are, and secondarily where the subjects are located. Anything done in the US or to Americans must take the Constitution into account. From an ethical perspective we might like to say that, just for instance, all people are created equal and are naturally endowed with certain unalienable rights, and so the US Constitution should protect the rights of all of humanity everywhere. There are,however, myriad practical and political problems with that view.
What is "private"?
Beyond jurisdiction, the other thing that determines the legality of information gathering is the question of privacy. Gathering public information is merely being well informed. Gathering private information is spying, or at least searching. And so the notion of an "expectation of privacy" enters the picture.
Current law holds that while the content of electronic communications such as phone calls and emails is generally protected (where US Constitutional and other protections apply), the addressing of the messages are not. The court generally has held that the average citizen has less of an expectation of privacy regarding the numbers called than regarding what is said. The address and return address on a postal envelope along with the postmark information is even less protected.
In the purely telephonic days, the devices that were used in this area were "pen registers" and "trap and trace devices". Pen registers recorded the numbers that a phone dialed. Trap and trace devices could determine and record the numbers from which incoming calls originated. These concepts have been adapted to digital messaging and networking. Thus, capturing and recording the addresses that computer traffic flows through is less protected than examining and recording the content of the messages.
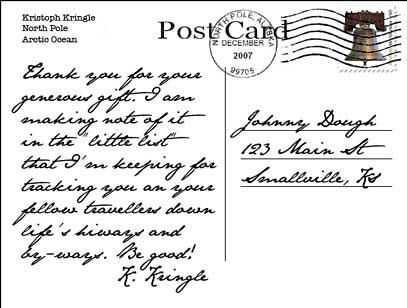
This brings us to the illustration of the post card that accompanies this article. Most Internet traffic isn't encrypted, and the address and data portion of a network packet are the same sort of things. In many ways, it is as if mail was accomplished with postcards rather than envelops. Imagine if you will, that the law applied to the information on a postcard the way it does to the Internet or phone call. Without a warrant, it is OK to capture and record the address and return address and the postmark information, but not the text.
Further, let us apply our assumptions above. If the sender and recipient are foreign nationals, operating outside the US, then it is OK for the intelligence services to read the whole postcard, but if either the sender or recipient is a "United States-person", then a warrant or other authorization is required. One can envision a peculiar device that covers the left half of the card or the handwriting on the left, exposing the printed return address, scans the address and postmark and determines the identity and location of the sender and recipient, compares that with suitable records and makes the decision as to whether the hidden portion can lawfully be photographed and recorded.
Mr. Kringle is a native of the North Pole, territory claimed by the Russians. Records show that the postcard arrived on a plane from Canada, but the postmark shows that before that it was mailed within the US. Young Mr. Dough is a US-person, possibly a US citizen. Before such phrases as "keeping a little list" and "fellow travelers" can be used as evidence that Mr. Kringle is a "Red", Mr Dough's rights must be accounted for.
My fanciful steam punk postcard scanner is actually not all that fanciful. It is rather analogous to the sort of software you would need to use in order to capture email. Email messages are just streams of bytes organized into packets and messages according to a whole hierarchy of standards and protocols, and the way that the addresses are encoded is not particularly different from the way that the message content is. In the outer couple of protocol layers,IP addresses are encoded in binary, but the to and from fields of an email message are encoded in exactly the same sort of human readable text as the body of the message. The most simple minded search programs that you could use to search an email stream could readily scan unprotected addresses and protected contents with equal ease.
To implement the intent of our laws, that foreign/foreign messages can be scanned, searched and recorded by our intelligence services, without a warrant or the involvement of the courts, but insure that US/US email requires an ordinary warrant and US/foreign-agent email can be handled in accordance with the FISA law, a moderately intelligent and carefully crafted program needs to be used.
Basically such a device would consist of a "pen register" to determine who the message addressed to and a "trap and trace device" to determine where it came from. An analyst or analytical engine of some sort then determines if at least one "US person" is involved, and if any foreign agents are involved. If both are "United States Persons", then a list of applicable warrants determines if the contents can be saved or analyzed. If no US person is involved, then the message can be freely analyzed. If a mixture, then a check for the FISA process must be made.
Any system for scanning the Internet trunk feeds that we have access must be very carefully controlled. The software wants to be carefully designed and implemented, and the people operating and maintaining it must be carefully vetted. The policies and procedures for authorizing and monitoring its use must be carefully written and and enforced with appropriate oversight.
Personally, if I were with the federal government, my approach would be to split the trunk and send the duplicate feed into a highly secured room, control who had access to that room, staff it only with people who had serious background checks, make sure there was a field manual and oversight. Given their charter, the combination of technology and surveillance would suggest that the NSA be the agency chartered to handle this. I'm thinking it would look a whole lot like the whistle-blower described. The question is can the feds be trusted? Given my dedication to civil liberties and my view on the lawless behavior of the current administration, I'd have to say, no, not in the current instant. But that doesn't mean that no US Attorney General and no National Security Adviser can be trusted. It just means that we know that they can't all be. We have illustrative examples.
Now a bunch of Senators, Representatives and the odd Presidential candidate probably have more faith in the notion that the federal government can be structured and run in a way that is trustworthy. In the end, most of us trust ourselves and some fraction of folks like us. So, with that in mind, how does the recently passed FISA amendment stand up?
What is the new FISA?
While working on this posting I've read Title I of the recently passed FISA amendment bill a couple of times and tried to chart out the differences. While doing so, I came across someone who has done the same thing and published his completed flow chart of the original and amended FISA, skipping the short-live Protect America Act. Let's have a look at his analysis along with the actual text. The original article can be found on Wes Walls' blog
Ketchup and Caviar. Here are the two flowcharts:

In his analysis, Wes says:
"The focus of change is the bolded red line marked “U.S. or non-U.S. Persons Located Inside or Outside the U.S.” Currently a warrant is required in this case. Notice the changes involving the bolded blue lines and text in the [second] chart. What New FISA does is create a special case involving our bold red line in the first chart. It provides a way for the executive branch to engage in warrantless (but “certified”) wiretapping of wire and cable (including email and phone) of any Foreign-to-U.S. communications collected inside the U.S. You’ll see the new set of criteria for certification in this special case. It does add new protections for U.S. Persons (citizens or greencard holders) by requiring the typical FISA warrant in all cases in which they are targeted."
I would have worded the change differently. What I would note is that the upper middle section of the flowchart changes from being based on location (the one rounded corner box and the three red lines) to a simpler pair of boxes based on whether any US person is involved. As a result, there is now a relatively simple three way decision regarding foreign surveillance. (Note that there is a fourth case, the "normal" one: If no foreign agents are involved, surveillance requires an ordinary warrant.)
- If any US person is involved or the communications is domestic, a FISA warrant is needed
- If no US person is involved, the communications is email or over cables, a special "Certification of Mass Acquisition" is available.
- Otherwise, no warrant is needed when no US person is involved.
Paths 1 and 3 represent the simple cases. One no US persons are involved and the communications is foreign, the foreign intelligence services are unencumbered by US law (#1). Generally, if the foreign intelligence services want to spy on Americans or in America, then a FISA warrant is needed (#3). One exception for this is allowed. Spying on electronic communications of non-US persons outside the US by means of surveillance inside the US can be done under the new "Mass Acquisition" process. Note that this is specifically the case where communications that is fair game to our spies is embedded in a system that is known to contain protected US communications that is not targeted. (This is pretty much my case where the combination of a pen register, trap and trace device and analytical engine can be used to separate the two.)
And that brings us to the blue box in the bottom right. Here's what Wes has there:
- Is the target reasonably believed to be located outside the United States?
- Is the purpose of the targeting to acquire foreign intelligence information?
- In the particular case, will "minimization procedures" adequately balance the privacy of US citizens against foreign intelligence needs?
- Will there be a good-faith effort to avoid domestic targets and domestic communications? Will other limitations be observed?
I've removed the struck out text and the pointer to
part II of "A Guide to the New FISA Bill". I will address these shortly.
Questions #1 and #2 basically reiterate the decisions that got us through the flow chart to Mass Acquisition. The new act's jurisdiction has gone from searches involving a "foreign power or agent thereof" to focusing on non-US persons outside the US (question #1). This is actually a good thing for the civil liberties of US persons, since as previously defined, a foreign agent could be a US person working for a foreign power. The question now is just "US person or non-US person". Without the struck out text, question #2 is basically a restatement of part of the logic that got us to this section. It becomes "Is the purpose of targeting [foreign communications between non-US persons believed to be outside the US by capturing traffic within the US] to target foreign intelligence information?"
With Question #3 we get to the heart of the issue, the "minimization procedures". These are spelled out in the bill in section 702 e, as follows (via
OpenCongress):
(e) Minimization Procedures- - REQUIREMENT TO ADOPT- The Attorney General, in consultation with the Director of National Intelligence, shall adopt minimization procedures that meet the definition of minimization procedures under section 101(h) or 301(4), as appropriate, for acquisitions authorized under subsection (a).
- JUDICIAL REVIEW- The minimization procedures adopted in accordance with paragraph (1) shall be subject to judicial review pursuant to subsection (i).
Section "301(4)", mentioned in #1 refers to physical surveillance, so the relevant section is 101(h), as follows (via
Thomas):
(h) “Minimization procedures”, with respect to electronic surveillance, means— - specific procedures, which shall be adopted by the Attorney General, that are reasonably designed in light of the purpose and technique of the particular surveillance, to minimize the acquisition and retention, and prohibit the dissemination, of nonpublicly available information concerning unconsenting United States persons consistent with the need of the United States to obtain, produce, and disseminate foreign intelligence information;
- procedures that require that nonpublicly available information, which is not foreign intelligence information, as defined in subsection (e)(1) of this section, shall not be disseminated in a manner that identifies any United States person, without such person’s consent, unless such person’s identity is necessary to understand foreign intelligence information or assess its importance;
- notwithstanding paragraphs (1) and (2), procedures that allow for the retention and dissemination of information that is evidence of a crime which has been, is being, or is about to be committed and that is to be retained or disseminated for law enforcement purposes; and
- notwithstanding paragraphs (1), (2), and (3), with respect to any electronic surveillance approved pursuant to section 1802 (a) of this title, procedures that require that no contents of any communication to which a United States person is a party shall be disclosed, disseminated, or used for any purpose or retained for longer than 72 hours unless a court order under section 1805 of this title is obtained or unless the Attorney General determines that the information indicates a threat of death or serious bodily harm to any person.
In essence, this is the requirements document for the pen register, trap and trace device and analytical engine device. Where as question #3 is "will the procedures be adequate?", question #4 is "will a good-faith effort be made to see that they are applied?" Two changes in the law would seem to attempt to speak to this question.
First, throughout the document, things that used to be the purview of the Attorney General or "the Attorney General
or the National Security Advisor" are now "the Attorney General
and the National Security Advisor" or at least "the Attorney General with the advice of the National Security Advisor". This doesn't guarantee the good intentions or competence of the two people, but it at least requires the collusion of two Senate approved officials, and one can see why the Senators might want that.
Second, the bill explicitly states in a number of places that the actions taken "shall be conducted in a manner consistent with the fourth amendment to the Constitution of the United States." This may seem frivolous. After all, all US laws must be consistent with the Constitution, and no federal action may legitimately violate Constitutionally protected rights. However, the inclusion of this specific proviso in the FISA law means that violations of the 4th amendment in carrying out these procedures is not only a violation of Constitutionally protected rights, with all that entails, but a federal crime under this statute as well. This provides an additional means of prosecution.
It remains to be seen whether these changes will have the beneficial effects that the Senators and others who support it hope, but I begin to see why they might think that this is an important improvement to the FISA laws. It
- brings all foreign surveillance under this law
- aligns the law with the jurisdiction and protections of the Constitution
- requires explicit procedures be defined for winnowing protected US communications from unprotected foreign communications
- makes the AG and NSA jointly responsible
- requires review
- makes explicit the criminal nature of stepping outside this law or the Constitution
- increases senate oversight
- makes explicit the grounds for criminal proceedings
While it may be argued that this law can be abused, that the government can use it as cover for domestic surveillance, the law explicitly addresses that. The law makes it a crime to target any of the following (from section 702(b)):
(b) Limitations- An acquisition authorized under subsection (a)-- - may not intentionally target any person known at the time of acquisition to be located in the United States;
- may not intentionally target a person reasonably believed to be located outside the United States if the purpose of such acquisition is to target a particular, known person reasonably believed to be in the United States;
- may not intentionally target a United States person reasonably believed to be located outside the United States;
- may not intentionally acquire any communication as to which the sender and all intended recipients are known at the time of the acquisition to be located in the United States; and
- shall be conducted in a manner consistent with the fourth amendment to the Constitution of the United States.
Making it a crime doesn't stop it, but it does give us a handle for dealing with it.
In the end, given the need to balance the Constitutional protections of US persons and anyone in the US with the need to allow the foreign intelligence services to spy on foreigners overseas, and the facts of the mingling of foreign and domestic traffic and that email is more like postcards than letters in envelopes, I am left wondering what alternative there is other than a law something like this one.